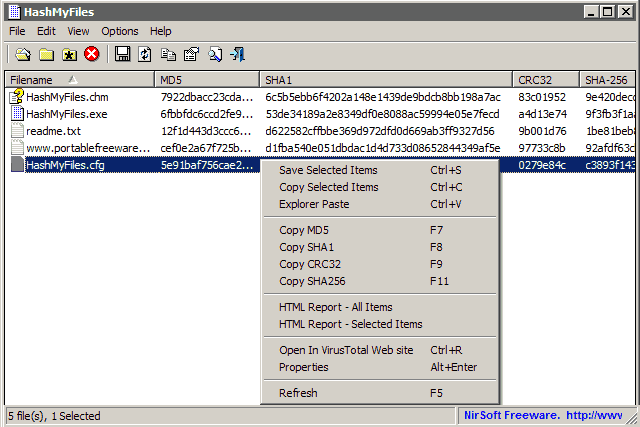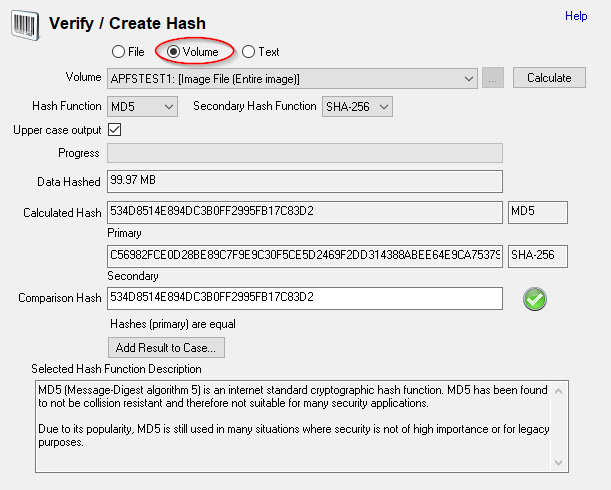
OSForensics - FAQs - How to check the MD5 (or SHA1) hash checksum of an entire volume, disk or image

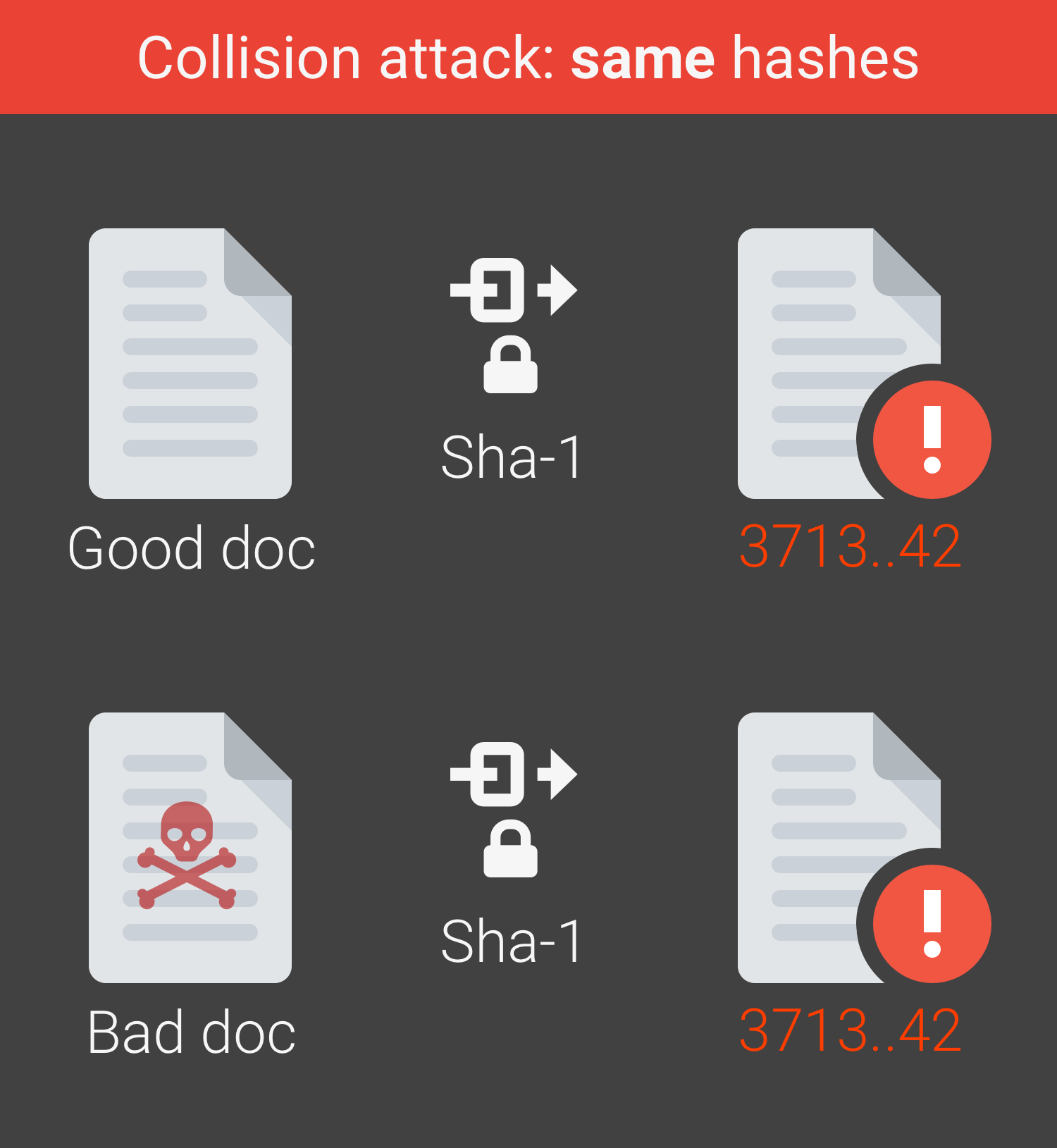
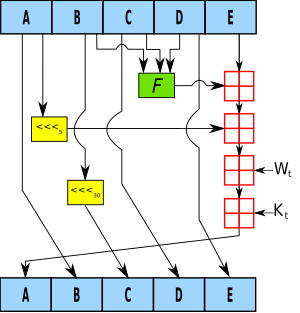
Integrating encryption techniques for secure data storage in the cloud - Seth - 2022 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
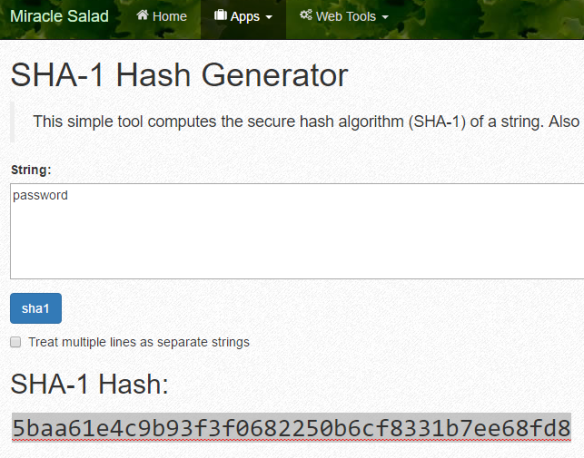
How to Crack SHA1 password hashes – online Crackstation – Visual guide | University of South Wales: Cyber University of the year: Three years running: 2019, 2020, 2021
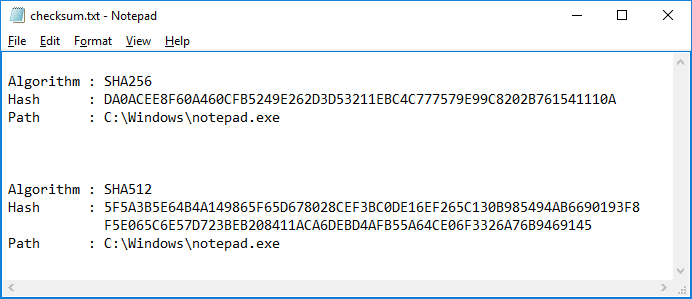
How do you determine the SHA-256 or SHA-512 checksum of a file? - ID: 109483101 - Industry Support Siemens
Free Online Tools for Developers, Testers, Project Managers, DevOps, and Security Testers | LambdaTest
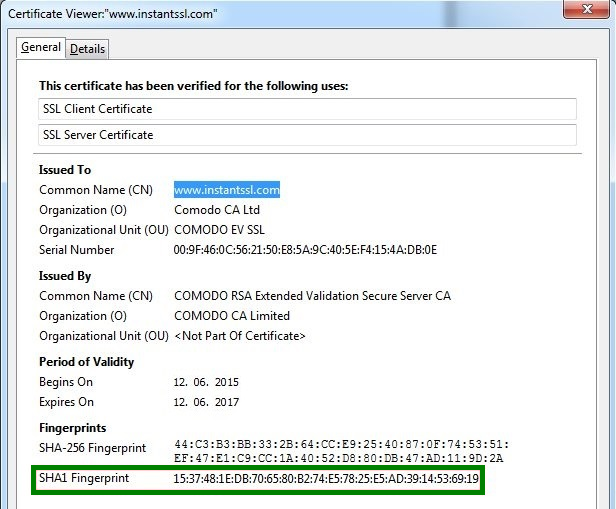
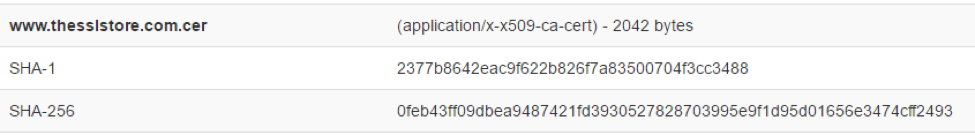
I can see SHA-1 fingerprint/thumbprint on my certificate. Is my certificate actually SHA-2? - SSL Certificates - Namecheap.com